Here there is a collection of useful download for your daily work. eBook, drivers, source code…

The best part of the Epic vs Apple trial is that the blast radius is so big that secret documents from the whole industry are being disclosed. The judge keep denying the futile attempts to seal the data. Look at this beauty (FB, Nintendo, Spotify, NFLX).
Original document Microsoft Word – 20-5640 – Epic Games – Trial Order No 1 Final.docx (courtlistener.com)
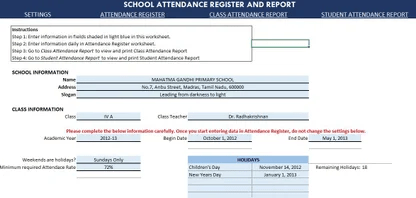
This Excel template can be used as an attendance register tool. You can create printable class and student attendance reports. This is ideal for use in schools and educational institutes. It can also be used at work places to track employee attendance. The template can track attendance for up to 50 students. You can customize your academic year (up to 366 working days). You can choose whether only Sundays or both Sundays and Saturdays are holidays. In addition, up to 20 school Holidays can be entered. You can set your own ‘pass requirement’ for attendance rate. You get ready to print Class and Student Attendance Reports. There are no macros in this template.


The tutorial shows how to create an Excel drop down list depending on another cell by using new dynamic array functions.
Creating a simple dropdown list in Excel is easy. Making a cascading drop-down has always been a problem. The above linked tutorial describes four different approaches, each including a crazy number of steps, a bunch of different formulas, and a handful of limitations relating to multi-word entries, blank cells, etc.
Here is the post.

This is an example file related to the post “How to change to sentence case in Excel“.
How to change a normal text to sentence case in Excel if we don’t have any function or option? In this port I explain how.

VICE is a program that runs on a Unix, MS-DOS, Win32, OS/2, Acorn RISC OS, BeOS, QNX 4.x, QNX 6.x, Amiga, GP2X, Dingoo, Syllable or Mac OS X machine and executes programs intended for the old 8-bit computers.
The current version emulates the C64, the C64DTV, the C128, the VIC20, almost all PET models, the PLUS4 and the CBM-II (aka C610).
If you have any comments or bug reports, please contact us at one of the addresses given below.
VICE is under constant change. Anyone interested in helping development of VICE is welcome. Please contact us to avoid doing something that someone else has done already. (-:
Of course our warm thanks go to everyone who has helped us in developing VICE during these past few years.

7th June 2020 – CBM prg Studio v3.14.0 released.
Well it’s been nearly two years since the last release (v3.13) of CBM prg Studio and so I’m really pleased to announce the release of version 3.14!
There’s a lot of new features and bug fixes in this version, and there’s a huge thank you to OldSkoolCoder for encouraging me to get back into this project and also helping with the new Git integration feature.
What Is It?
CBM prg Studio is a Windows IDE which allows you to type a BASIC or machine code program and convert it to a ‘.prg’ file, which you can then run in an emulator or on real hardware. It also includes character, sprite and screen editors and a fully featured 6510/65816 debugger.
The following machines can be developed for:
- Commodore 64 (and SuperCPU)
- Commodore 128
- Commodore VIC 20
- Commodore 16
- Commodore Plus/4
- Commodore PET BASIC 2 machines, e.g. PET 2001
- Commodore PET BASIC 4 machines, e.g. PET 4000/9000
What CBM prg Studio isn’t is a front-end for tok64, cbmcnvrt, bastext or any other tokeniser/detokeniser/assembler. It’s all been written completely from scratch.
Follow the download link for more details.


This is the User Manual for THEC64, with full details on how to use all of the functionality, including VIC 20 mode and Media access.
For Warranty information, please visit the warranty page.

If you want to show how multiple units does comparison to each other based on the same criteria clearly, you can use the positive negative bar chart which can display positive and negative development very good as below screenshot shown.

In Excel, it may be easy for us to highlight the cells based on a specific text, but, here, I want to highlight a specific text within a cell to make it outstanding but not the entire cell. This maybe a troublesome for most of us. This article, I will talk about some tricks for solving this job in Excel.
This file contains an Excel file with macros. Read my post here.

If you haven’t played Jumpin’ Jack or want to try this action video game, download it now for free! Published in 1984 by Advantage Computer Accessories, Inc., Jumpin’ Jack was an above-average arcade title in its time.







Each resource or service type in Azure enforces a set of naming restrictions and scope; any naming convention or pattern must adhere to the requisite naming rules and scope. For example, while the name of a VM maps to a DNS name (and is thus required to be unique across all of Azure), the name of a VNET is scoped to the Resource Group that it is created within.
This spreadsheet helps you to define the name (URL) for each resource.
R for Data Science – Import, Tidy, Transform, Visualize, and Model Data
R Packages by Hadley Wickham O’Reill
CSV file for a desk of card
Use this Registry file to reset the external display cache in Windows 10. It removes the following entries in the Registry:
- [-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\GraphicsDrivers\Configuration]
- [-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\GraphicsDrivers\Connectivity]
- [-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\GraphicsDrivers\ScaleFactors]
MGI research combines the disciplines of economics and management, employing the analytical tools of economics with the insights of business leaders. Our “micro-to-macro” methodology examines microeconomic industry trends to better understand the broad macroeconomic forces affecting business strategy and public policy. MGI’s in-depth reports have covered more than 20 countries and 30 industries. Current research focuses on six themes: productivity and growth, natural resources, labor markets, the evolution of global financial markets, the economic impact of technology and innovation, and urbanization.
May 26th, 1995: Bill Gates sends a memo, entitled “The Internet Tidal Wave,” to all executive staff within Microsoft. In it, he makes clear his intention to focus the company’s efforts online with immediate effect and “assign the Internet the highest level of importance,” going on to call it, “the most important single development to come along since the IBM PC was introduced in 1981.”

This eBook provides guidance on how to implement the Model-View-ViewModel (MVVM) pattern, dependency injection, navigation, validation, and configuration management, while maintaining loose coupling. In addition, there’s also guidance on performing authentication and authorization with IdentityServer, accessing data from containerized microservices, and unit testing.
